Detecting and responding to insider threats
Insider threats vary from harassment of co-workers to sabotage and theft. Proprietary or client data may be leaked or sold, access credentials stolen, and company systems wiped or crippled with malicious code. These threats are identical to those from outside actors, but they come from trusted employees.
Monitoring social media allows security professionals to pick up threats before they become serious.
In 2017, a Pennsylvania convenience store worker shot and killed three of his colleagues before turning the weapon on himself. Investigators later discovered he had posted extensively online about his plans and motivations. This is an extreme case, and, while the danger from insider threats may not always be so violent, they can pose as much of a risk as threats from outside.
Insider threats take many forms
Insider threats vary from harassment of co-workers to sabotage and theft. Proprietary or client data may be leaked or sold, access credentials stolen, and company systems wiped or crippled with malicious code. These threats are identical to those from outside actors, but they come from trusted employees.
No organization is immune. In 2017, Wikileaks began publishing secret CIA files in an archive known as Vault 7. It was soon discovered a former CIA software developer was responsible.
Many of these insider threats leave an online fingerprint, albeit faint. Not every warning sign is as splashy as an online manifesto. Some may be as commonplace as social media posts about a business or an employee. Others may be more difficult to see. In some cases, stolen data is traded on dark web marketplaces or shared in unindexed platforms such as Telegram.
A risky time for employers
Most economies have experienced a slowdown to the post-pandemic rise in employment. Many are experiencing stagnant or negative growth. Job market uncertainty increases the likelihood of insider threats. Disgruntled employees are more likely to stay in roles and express frustration internally. When layoffs loom, the emotional and financial impact of job loss can push some individuals toward harmful behavior of various types – from sabotage to violence.
Open Source Intelligence is a powerful tool
Open Source Intelligence (OSINT) plays a crucial role in identifying and mitigating these risks. Monitoring social media allows security professionals to pick up threats before they become serious. An advanced tool such as Signal, helps security teams overcome the challenges of monitoring the vast amount of information found online.
Using custom searches, AI-assisted alert triage, and event summaries, Signal allows security teams to pick up threats, in real time. Because insider threats seldom telegraph their presence at work, it is difficult to target particular individuals. But OSINT tools, such as Signal, monitor comments, sentiment and direct threats to organizations, unearthing internal as well as external threats.
Key risk points in the employment cycle
The end of employment is a critical time for insider threat monitoring:
While most of these employees don’t pose a serious risk, having extra notifications and searches in operation during layoffs or restructuring helps improve situational awareness.
Some insider threats emerge only after the damage is done. OSINT tools can also help uncover these incidents by monitoring suspicious activity in locations such as the dark web or unindexed platforms. If employees were planning to sell or trade sensitive data, then the right OSINT tool looking in the right places may be able to detect malicious activity. Armed with this knowledge, security teams can take action to mitigate damage and even provide vital information for the apprehension or prosecution of bad actors. Signal has the capability to monitor dark web forums for this sort of behavior, as well as unindexed areas of the internet such as Telegram or Discord.
Damage can be far-ranging
While violence grabs headlines, insider threats often cause lasting financial, operational, and reputational damage. Organizations may be held liable if they fail to take reasonable steps to prevent or mitigate insider actions. Having the right OSINT tools in place and utilizing them effectively is an excellent first step in detecting and mitigating insider threats.
Summary
Insider threats exploit the trust organizations place in their employees. With the right tools, security teams can detect trouble early and respond proactively.
Signal offers broad and deep OSINT coverage across a range of sources, including forums, blogs, as well as the surface, deep and dark web. Real-time custom alerts combined with AI-enhanced detection, triaging and reporting help security teams act fast.
To find out more about how Signal can protect your organization against internal and external threats, book a Signal demo today.
What’s happening in executive protection? How OSINT can help
Good executive protection reduces liability risks and protects organizational reputation. As the public face of their companies, an incident involving an executive can undermine confidence among investors, customers and employees alike.
On 4 December 2024, the CEO of United Health, Brian Thompson, was shot and killed on a New York street. Suddenly, executive protection became a hot topic among business leaders around the world. What had previously been a "nice-to-have" suddenly became a necessity.
A year later, Signal's US distributor, Everbridge, has sponsored a report from ASIS (a global community of security professionals across industries and disciplines) that examines the current state of executive protection. The report, The Executive Threat Environment: Benchmarking Research on Risk-Based Approaches to Executive Protection, is a wide-ranging document with data from over 400 security professionals and 100 security consultants worldwide.
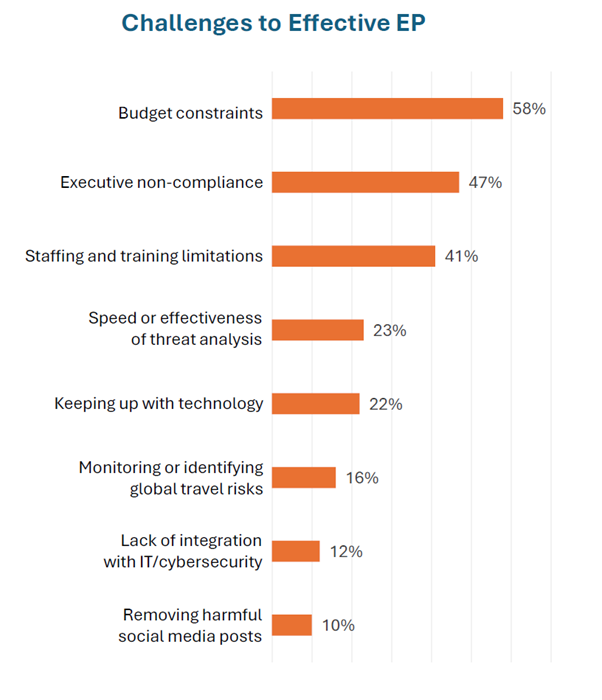
For many corporate security teams, these findings highlight familiar challenges: limited budgets, inconsistent policies and uneven executive buy-in. The report also contains valuable information for anyone considering the role of Open Source Intelligence (OSINT) in their security toolbox.
A growing focus on executive protection
It's not a huge surprise to see that 42% of security professionals surveyed by ASIS saw a significant increase in focus on executive protection. When we dig into the reasons, the connection to recent events, such as the New York assassination, becomes even clearer. High-profile incidents are cited as a driver by 69% of the security professionals surveyed. A general increase in public threats (72%) and specific threats to executives (61%) paint a strong picture of a threat environment that is now capturing the attention of corporate decision-makers.
What are security professionals doing about it?
Despite the risks, major gaps remain in executive protection. Only 55% of those organizations with 100,000 or more employees (or students) had a formal executive protection policy. That number drops to just 26% among those with fewer than 50,000 staff or students.
This shortfall may stem from misconceptions about what executive protection actually involves. Many professionals still associate it solely with physical security details. But, as one ASIS respondent put it:
“…true executive protection is a proactive risk-management discipline that blends intelligence, logistics, behavioral analysis, medical preparedness, and operational planning to ensure the principal's safety without disrupting their lifestyle or productivity.”
The importance of executive protection
The renewed focus on executive protection may also be due to a realization from corporate leadership of the benefits that it offers beyond physical security. Good executive protection reduces liability risks and protects organizational reputation. As the public face of their companies, an incident involving an executive can undermine confidence among investors, customers and employees alike.
Effective executive protection can also help attract and retain top talent. Demonstrating that the organization takes leadership safety seriously sends a strong signal about its values and professionalism, another tool for competing for the very best leadership talent.
The role of OSINT in executive protection
The ASIS report examines the technical capabilities necessary for effective executive protection, with online threat monitoring ranked as the most important capability. Of the more than 500 security professionals and consultants surveyed:
65% said online threat monitoring was important, but only 51% of respondents believed they had full capability.
Real-time OSINT was ranked as almost as important (63%), yet only 50% of those surveyed believed they had full technical capability.
Of those organizations that had the technical capability, OSINT (82%) and social media monitoring (79%) were the most used methods to identify and assess threats. So, if these are the most used methods, why aren't all organizations using OSINT for executive protection?
One of the biggest challenges comes from executives themselves
One of the findings of the report of interest to those outside security circles, but unsurprising for those on the inside, is that executives are one of the biggest hurdles. Those surveyed identified the top two concerns were:
Budget constraints (58%).
Executive non-compliance (47%).
Data to build a business case
In the absence of sensational headlines, security professionals need to build a business case to expand their capabilities. And the best way to build a business case may lie with OSINT tools themselves. Currently, less than half of security professionals surveyed in the report provide comprehensive data to leadership to justify their requirements. Only 41% considered data logging and exportable analytics to be essential capabilities for their executive protection, and only 25% regarded automated after-action reports as necessary.
That’s a missed opportunity. Measurable data can demonstrate return on investment, showing that effective protection prevents incidents rather than simply responding to them.
Good OSINT provides good data
The AI-enabled reporting of products like Signal provides security teams with the data they need to strengthen their cases and further enhance technical capabilities. Using AI, Signal compiles summaries and reports for leadership to demonstrate the extent of threats and the effectiveness of proactive actions taken to mitigate risk.
Having AI as part of the tool reduces the workload on an organization’s team to provide the reports, freeing them up to make the proactive interventions necessary. Signal is also cost-effective, providing real-time, scalable OSINT. The coverage is broad, allowing security teams to have eyes in locations where they can't be physically present.
Effective OSINT yields additional ROI across the organization. It can inform travel planning and reputational management, ensuring a greater "bang for buck" and allowing security teams to have input in other areas of executive protection that go beyond close physical protection.
Summary
Using tools such as Signal gives security teams important capability in real-time OSINT and provides valuable data to build business cases for enhanced protection. The case can’t be built on fear alone. The ASIS report carries some valuable advice for any security professional wanting to make the case for better executive protection:
"Avoid using fear-based messaging. Instead, communicate the value of protection in terms of business continuity, reputation management and operational efficiency.
Build trust by being discreet, professional, and solution-oriented. Involve them in decision-making processes, offer options rather than ultimatums, and always back your recommendations with clear, real-world examples and risk intelligence. Ultimately, the key is to position security as an enabler—not an obstacle—of their success."
With the right data and tools, security teams can build stronger, smarter protection programs.
When you're ready to join those security professionals who see the real value of quality, comprehensive, and real-time open-source intelligence, we're ready to talk. Book a Signal demo today.
7 Dark Web Forums You Need to Monitor for Improved Cyber Security
We take a look at how security professionals can utilize OSINT tools like Signal to more efficiently and effectively monitor threats on dark web forums.
The dark web has grown in popularity over the years, as people become increasingly technologically savvy. Using a darknet browser like Tor or I2P enables users to remain anonymous while browsing the internet.
People seek anonymity online for many legitimate reasons. For example, they might have concerns about large companies' abilities to track their online activity, or they might not feel comfortable giving Google all their data. Alternatively, they might live in a place with restrictions on freedom and free speech and necessarily turn to dark web anonymity to access world news or freely share journalism.
However, that same anonymity also protects criminals. It allows them to operate across borders, organize crime and trade in illegal items, both physical and digital. Dark web forums also host discussions on topics including extremist ideas, hate speech, threats of violence, or even plans for cyberattacks.
This wide range of dark web activity is a key concern for security professionals. By monitoring the dark web with OSINT tools, such as Signal, security professionals can discover exploit kits targeting their organization, get early alerts of data breaches, and even prevent physical attacks on assets or employees.
In this article, we examine a few of the more common dark web forums and explore how security professionals can utilize OSINT tools, such as Signal, to more efficiently and effectively monitor threats on the dark web.
About dark web forums as data sources
Because of the anonymity afforded by the dark web, people feel comfortable discussing all manner of things. As such, the dark web – especially dark web forums – is a valuable source of intelligence for security professionals. Monitoring these channels can help expose real and potential threats, ranging from planned attacks, both physical and digital, to fraud, data breaches and more.
Below, we examine 7 of the largest dark web forums that professionals should be aware of as potential sources of security data.
BreachForums
Despite multiple takedowns by law enforcement and rumours that it may now be a ‘honeypot’ (a site compromised by law enforcement or security researchers), BreachForums and the mirror sites that pop up are still a major threat. BreachForums and its mirrors are still one of the most visible places for selling or leaking corporate databases and credentials. If your company data is compromised, it is highly likely it will appear here.
DarkForums
This is a relatively new forum, emerging as a successor to BreachForums. With a rapidly growing user base, this English-language site specializes in data leaks, malware and access sales.
Cracked / Nulled
Cybercriminals mostly use these forums to trade and purchase leaked or hacked information. Despite a significant law enforcement action in mid-2025 (Operation Talent), these forums still have millions of members. They are able to remain in operation in much the same way as BreachForums, by spawning mirror sites.
Dread
Dread is a forum on the darknet that mirrors Reddit’s functionality. It provides the same familiar community discussion boards. The forum takes many ideas from Reddit, such as sub-communities and user moderation responsibilities. The site mimics this functionality without any JavaScript. The primary goal of Dread is to offer a censorship-free forum; however, it also provides hacking guides, software and carding tools, as well as drugs and stolen data. Dread also serves as a place for news on the latest dark web marketplaces.
XSS
A longstanding Russian language forum. XSS has a reputation for high-quality content and is a closed forum with restricted access to approved members. Access to compromised systems is frequently sold and traded on this site.
Exploit
Exploit has been in existence even longer than XSS, for many of the same reasons (high-quality content and restricted access). Due to its longevity, most types of cybercriminal activity can be found in dedicated sections.
RAMP
This is another Russian-language forum that has quickly gained prominence on the dark web. It functions as both a forum and a marketplace for criminal activity with a particular focus on financial fraud.
Other prominent forums
Other active forums with substantial membership include:
LeakBase
Crax
Germania (a German-language forum)
Infinity
HackForums
Sinister.ly
Mirror sites for older forms, such as RaidForums, also persist on the dark web.
The dark web is no longer the only location for this type of activity. Apps such as Telegram and Discord, which sit on the unindexed deep web, are also becoming increasingly popular for cybercriminals to trade exploits, swap information and organize activities.
Related: How Can 4chan be Used as a Data Source for Security Intelligence?
Why dark web monitoring is difficult
Security professionals face numerous challenges when it comes to monitoring the dark web. For a start, there is the sheer volume of posts. With each of these forums and marketplaces operating across numerous time zones, they experience continuous activity. The most popular get tens of thousands of posts a day. Manually monitoring these sites is just not a feasible task.
Secondly, the fluid nature of the dark web community means that forums and marketplaces are forever becoming the victims of law enforcement action, internal troubles or scams. For example, XSS may have become compromised even as this blog is being published. These forums and marketplaces are like a Hydra – when one is cut off, new sites or mirror sites sprout up almost immediately.
Thirdly, the more explicit dark web forums and marketplaces (such as XSS or Exploit) will require you to create an account and may even go some way to verifying that you have the necessary skills to be allowed in. While the anonymity of the dark web means administrators of these forums likely can't work out exactly where you came from or what your true purpose is on their platform, those that are interested might attempt to determine your real identity. When creating an account, it’s essential to make sure it holds no relevance to any other online account you have, if you want to maintain your complete anonymity and avoid becoming a target of those same criminals you are looking to monitor.
Once inside, you must remain active on the platform without arousing suspicion; otherwise, your hard-won access could be revoked.
Finally, a lot of hackers on the dark web would be more than willing to turn their talents and attention to you, should you accidentally cross them. Some websites will infect your device with malware, so treat all links or downloads with suspicion. Additionally, clicking those links may take you to disturbing material. So, unless you’re confident you can safely and securely navigate the dark web, it may be better to look for safer, more efficient alternatives.
How Signal makes dark web monitoring safer and smarter
The Signal OSINT platform works by continuously scanning the surface, deep, and dark web. You can run custom Boolean searches across multiple data sources. These search results can then be filtered using our advanced AI and natural language processing (NLP), which enables you to search across languages, determine location, analyze copy in images and even assess the emotional intent behind text through our NLP software, Spotlight.
The benefits of having a tool like this for monitoring the dark web include efficient, continuous monitoring and assessment of a multitude of sites, allowing security teams to monitor more of the web to catch more threats faster. Because Signal’s searches are across the dark web, rather than specific sites, they do not rely on security teams having up-to-the-minute intelligence about which forums or marketplaces are active and popular. Additionally, security professionals can access this data without ever having to hunt down and access the various dark web forums and marketplaces, which is both more secure and much more time-efficient.
This lets you automate dark web monitoring – cutting costs, while expanding coverage and relevance.
5 Dark Web Marketplaces Security Professionals Need to Know About
We take a look at how security professionals can overcome the plethora of challenges that come with finding, accessing, and efficiently monitoring dark web marketplaces for information security.
Dark web marketplaces are online platforms, where people can buy and sell illegal goods and services while remaining anonymous. The offerings include leaked credit card details, exploit kits, hackers for hire and advertisements for hitman services.
Because of the range of goods and services available, as well as the conversations that occur around these transactions, dark web marketplaces can be immensely valuable sources of data on criminal activity. As such, they are typically under intense scrutiny from both law enforcement and security professionals.
These marketplaces have become increasingly sophisticated, with slick user interfaces that resemble familiar online storefronts, such as Amazon, along with seller ratings and escrow services for secure payment. This makes the barrier for users lower than ever before.
5 dark web marketplaces
People have been organizing illicit trades via the internet since the 1970s. Those early examples were through closed networks, with actual exchanges of money and goods usually taking place in person. With the advent of cryptocurrencies, it has become easy to complete online trades without leaving a trail. As a result, the online trade of illegal goods has become increasingly commonplace, and vast dark web marketplaces have emerged.
The very first of these marketplaces to pair the darknet with Bitcoin was the Silk Road, created by Ross Ulbricht in February 2011. Over the following two years, the Silk Road set the standard for dark web marketplaces. By the time it was shut down in October 2013, and Ulbricht arrested, the site had traded an estimated $183 million worth of goods and services.
Torzon Market
Torzon is one of the largest general-purpose darknet markets still active in 2025. It offers a familiar mix of narcotics, fraud tools and digital services. The site operates on Tor and supports Bitcoin and Monero, utilising escrow to facilitate transactions. Torzon also imports vendor feedback from other platforms, providing some continuity for buyers and sellers who have migrated after past shutdowns.
STYX Market
STYX has carved out a role as a hub for stolen data rather than drugs. Its listings focus on stealer logs, initial access and financial credentials, making it highly relevant for financial security professionals. Unlike older drug-oriented markets, STYX looks more like a specialized cybercrime exchange than a bazaar.
STYX is a great example of a ‘new model’ market with a searchable structure and trusted vendor processes, which helps buyers quickly filter for fresh data. The market grew through 2023-24 and remains active in 2025, underscoring how access and credentials have become commodities on par with drugs in the dark web economy.
Russian Market
Often written as RussianMarket, this is the largest marketplace for stealer logs. It aggregates credentials, cookies and session data harvested by malware such as RedLine, Raccoon and Vidar, and sells them in bulk. This makes it both a goldmine for attackers seeking account takeovers and a persistent monitoring target for security professionals.
Researchers estimate that millions of logs are for sale, with new ones added daily. Its endurance shows how cybercriminal demand has shifted from physical contraband to stolen identity data. For enterprises, Russian Market illustrates why compromised credentials remain one of the most common entry points for intrusions.
2easy
Sometimes branded 2easy.shop, this site has become known as the budget marketplace for stolen logs. Rather than focusing on premium access, it thrives on low-cost, high-volume sales. Individual log packages are often priced between $5 and $25, making them accessible to a wide spectrum of buyers. 2easy's persistence highlights the democratization of cybercrime. Criminals no longer need large budgets to obtain working credentials, just a few dollars.
BriansClub
BriansClub is a long-running carding shop, best known for selling stolen credit card ‘dumps’ and CVVs. Despite a 2019 breach (and law enforcement action) that exposed millions of its records, the shop has remained active and continues to attract buyers in 2025.
Estimates before the breach suggested a nine-figure annual turnover and, while its exact scale today is harder to verify, it remains one of the most recognisable carding brands.
Other markets include Abacus market, BidenCash, Exploit, Exodus Marketplace and more.
The diffusion of dark web marketplaces
With the rise of encrypted communication apps, such as Telegram and even Discord, some of the trade previously undertaken on the dark web has ‘surfaced’ to the unindexed deep web. Channels such as CrdPro Corner, AsCarding Underground and Daisy Cloud are flourishing on Telegram, with thousands of users in each channel trading everything from logs to bots. These channels often operate as subscription services, providing fresh dumps of material daily.
How to keep track of evolving darknet marketplaces
There are various active dark web marketplaces. One of our data providers estimates there are approximately 20 active, leading dark web marketplaces and dozens of smaller, additional marketplaces. With the diffusion to the unindexed deep web, this number becomes even greater.
Gaining access and monitoring these darknet marketplaces comes with a unique set of challenges. Firstly, they generally have short lifespans. This could be for a variety of reasons. For example, law enforcement might close them down; or, perhaps to help avoid this fate, they frequently change their domain address. It could even be because the admin implemented an exit scam, as happened with Empire Market, where the admin team is estimated to have made off with approximately $30 million worth of Bitcoin in August 2020. Almost none of the marketplaces featured in the 2020 version of this article are in existence now.
Due to this short lifespan, security professionals need to constantly be on the lookout for the next big marketplace. However, because of the illicit nature of the dark web, many websites don’t want to be found; as such, there is no easy way to navigate the dark web. Each website can be thought of as an independent silo. Darknet websites rarely, if ever, link to one another. To find forums and marketplaces on the dark web, as well as in the deep web, you need to know what you’re looking for and how to look for it.
Finally, once the relevant sites have been located and access gained, there is still the serious challenge of monitoring the dark website to gather usable intelligence effectively. Doing this manually requires vast amounts of resources; however, you also can't simply scrape the website, as such activity can quickly get you banned from a site.
This is where Open Source Intelligence (OSINT) tools like Signal come in.
The role of OSINT tools when monitoring the dark web
OSINT tools allow security professionals to effectively and efficiently monitor the surface, deep and dark web. Using Signal, you can create targeted searches with Boolean logic and run the results through intelligent filters powered by our advanced AI. The process can be automated with real-time SMS and email alerting.
This reduces the need for skilled professionals to spend all their time manually monitoring the entire web and assessing the associated risks. Additionally, it reduces the inherent risk of accessing criminal forums and marketplaces. Instead, security professionals get hyper-relevant alerts that can quickly be assessed and acted upon without ever actually having to go onto the dark web or painstakingly gain access to marketplaces.
This approach is vastly more time-efficient and allows you to put your web monitoring on autopilot; reducing costs, while simultaneously increasing efficacy. As cyber-criminals embrace new technologies, it’s becoming increasingly necessary for security professionals to do the same to stay ahead.
Increase the scope of your monitoring ability and the overall amount of hyper-relevant intelligence at your fingertips. Gather actionable intel in real-time.
The Threat of Doxing to Organizational Security
Organizational doxing is on the rise and can be immensely damaging, exposing company secrets and customer data, or more directly exposing executives to new levels of threats.
What is Doxing?
The term itself originates from the phrase “dropping docs” and was later shortened to “docs” and then “dox”. As the original term suggests, doxing is when someone collects and then shares information about another person or organization.
There are numerous reasons someone might dox someone else or be the victim of doxing. It could be for revenge or a personal grudge, a disgruntled ex-employee might target their previous employer, for example. In 2014, Sony was the victim of a doxing attack backed by, experts believe, the North Korean government after they released a film which made fun of their leader. Other motivations include harassment and cyber-bullying, vigilante justice (for example, exposing neo-Nazi’s), and doxing for financial gain.
Organizational doxing is on the rise and can be immensely damaging, exposing company secrets and customer data, or more directly exposing executives to new levels of threats.
Doxing Strategies and Goals
Traditionally doxing started with an online argument escalating to one person digging out information on their adversary and sharing it online. More recently though, doxing has become more of a cultural tool with hackers taking down people or groups with opposing ideologies. When it comes to organizations, threat actors have been known to both target an organizations reputation and to use information gained through a doxing attack to leverage financial reward.
For example, in one scenario an employee at a bank was blackmailed after a doxing attack into using his position in the bank to steal over $100,000 from customers for his blackmailers.
The fallout is generally reputational with the victim suffering from online abuse such as death threats to them and their family in lieu of the new information shared. However, on occasion, the fallout can be significantly worse. There have been examples of mobs dishing out physical vigilante justice after a person's information, such as an address, was shared online.
There are numerous ways you can be identified online. By following ‘breadcrumbs’ of information a dedicated doxxer can assemble an accurate picture of a person - even if they were using an alias. The kind of details they might look for include, full name, current address, email address, phone number etc. Additionally, some doxxers might buy information from data brokers.
IP/ ISP Dox
There are various methods that can be used to locate your IP address, which is linked to your location. With just your IP address a doxxer could then use social engineering tactics against your Internet Service Provider (ISP) to discover the information they have on file such as:
Your full name
Email address
Phone number
ISP account number
Date of birth
Exact physical address
Social security number
This requires the doxxer to go through a dedicated process, which may not even work, however, it’s just one strategy they can employ, and even if they are unable to gather further information through a gullible ISP worker they still have the first parts of the puzzle - your IP address and a rough location.
Doxing with Social Media
If your social media accounts are public then anyone can view them. Often things a threat actor can find out include your location, place of work, your friends, your photos, some of your likes and dislikes, places you’ve been, names of family members, names of pets, names of schools you attended, and more.
With this kind of information, they can then find out even more about you, or even discover the answer to your security questions helping them break into other accounts such as your online banking.
As such it’s recommended to keep your social media profiles private, and if you use multiple online forums to use a different name and password for each to help prevent doxxers from compiling information from across multiple online forums and social media sites.
Data Gathered through Brokers
Data brokers on the internet collect information from publicly available sources and then sell the data for profit. Generally speaking, they sell this data to advertisers - if you’ve ever found yourself randomly receiving emails from companies you’ve never heard of before, this is why. However, for a doxxer it could be an easy way to start building a detailed profile of their target.
How Might Doxing be Used Against Your Organization?
For organizations to be successful with their media strategies they necessarily need to share relevant information and regularly engage with their customers through social media channels. This provides a substantial opportunity for doxxers.
By combining publicly-available data with basic attack techniques, such as phishing campaigns or credential stuffing, malicious actors can uncover large quantities of supposedly secure data. For consumers, exposed information could lead to identity theft or public shame. Meanwhile, companies face the prospect of large-scale reputation damage or lost revenue if proprietary project briefs or intellectual properties are leaked to the public.
Additionally, doxing can be used as an incentive to expedite the resolution of ransomware attacks. This is where the cyber attacker threatens to release documents or information to the public should their target not pay the ransomware fee promptly. This adds to already serious financial implications.
How Can you Prevent Doxing?
Unfortunately, it's nearly impossible to completely remove personally-identifying information from the internet, especially parts which are part of public records. Still, there are some tips to reduce your attack surface.
Keep your profiles private
People and organizations do have a lot of say as to what gets published on the internet. Make sure to practice general data privacy best practices.
Avoid posting identifying information
Keep all social media settings at the most private level, and don't accept friend requests from people you don't know
Change the settings on Office and your phone's photo app so personal info isn't embedded in those files
Use a "burner" email address for signing up for accounts when possible.
Set the ‘whois’ records on any domains you own to private
Ask Google to remove personally available information about you, and request the same from data broker sites
Implement Safe Browsing Measures
These steps are good internet hygiene in any case, but can also prevent a breach that can lead to your info being exposed to a potential doxxer:
Use a VPN, especially when using insecure public Wi-Fi networks
Switch to a secure email system with built-in encryption
Vary your usernames and passwords
Self-Doxing
Humans remain the weakest link in the security chain. In most cases, malice isn’t the problem or the intent when someone lets a threat actor in. Instead, employees overshare personal data on corporate platforms by accident or use insecure third-party applications. In both cases, however, following the breach and identifying the potential compromises is difficult when IT teams start from the side of defenders.
By flipping the script and looking at your organization from the view of potential doxxer it becomes easier for IT and security teams to spot key areas of weakness. They can then develop strategies and staff training programs to protect against them.
Final Words
Doxing represents a growing threat to organizations and individuals. However, by self-doxing with security intelligence gathering strategies, security teams can create accurate attack surface maps. With this intelligence, they can then enhance threat modelling and deliver actionable insights to staff to reduce overall risks.
Using OSINT software like Signal you can learn about potential threats as or before they occur, learn about potential exploits targeting your organization, and self-dox to help identify weaknesses and shore-up defences.
Leveraging Telegram as a Data Source for Open Source Intelligence
Conversations on public Telegram groups can offer valuable insights into ongoing and potential criminal activity making it a valuable data source for security professionals.
People are increasingly aware of how their data is accessed and used, whether this is the security of their private conversations, their online browsing history, or even Personal Identifiable Information (PII). With this increase in consciousness for data privacy, chat applications have had to promise better encryption and anonymity if they are to compete.
As such, over the last few years new chat apps, with a primary USP of better privacy have hit the market. This includes the likes of Telegram and Discord. The anonymity and data security offered by these apps have quickly made them popular with both legitimate users and criminals. On Telegram, you don’t have to look too hard to uncover conversations around the sale of illicit goods, examples of extremist views and hate speech, the trading of PII, and more. It’s also worth noting that many marketplaces and forums on the dark web also have chat groups on Telegram.
Many of the groups and channels on apps like Telegram are open to the public, allowing users to easily reach a large potential market relatively risk-free. Not all groups though are open to the public making it substantially harder for security professionals and law enforcement to monitor these channels successfully.
However, with a tool like Signal, you can view and monitor data from many of these closed communities and hard to access groups easily and efficiently.
About Telegram
Telegram is a messaging app that was launched in 2013. It focuses on supplying a fast, free and above all, secure messaging service. The chat app has end-to-end encryption and several other features which add to it’s perceived security. These features include “secret chats” which store data locally, a timer on messages to self-destruct after a specified time, notifications of screenshots, and messages in secret chats can’t be forwarded. Their main USP is to provide a service where data is protected from thirds parties, including any curious government or security agencies.
Unlike other chat apps, Telegram promotes itself as providing its users with full anonymity, including the ability to set up a unique username and make your phone number to private. It’s because of these security features as well as the offered anonymity that the application quickly became a popular choice for criminal communications.
How Can You Leverage Data from Telegram for OSINT?
There are various channels and groups on the Telegram app in which illicit and criminal activity is discussed or undertaken. This ranges from the sale of illegal goods, stolen data, to planning physical attacks on an organization or individual.
For example, on the group “Carders” on Telegram, a group which has over 5,000 members you can find stolen credit card details including full numbers and CVV codes. This chat group is linked to an online shop getbette.biz (which was taken down in early 2020). Most of the conversations in this group revolve around some form of financial fraud, whether that’s leaked card details or the sale of PII.
On other Telegram groups, you can find details for hacked personal accounts like Netflix, Disney Plus, Amazon Prime etc. These logins might be sold for a variety of reasons, such as credential stuffing, or for personal use.
It’s not just dealing in illegally obtained data though. Telegram is used for a broad variety of purposes. A particularly popular one is the sale of drugs. Narcotic Express DE is one such group. With close to 1,000 members, this German group is a closed group which focuses on the purchasing, sale and distribution of drugs.
Closed groups cannot be found in a search within the app or in the dedicated Telegram search engine, instead, you have to be invited and sent a link by another user in the group. In addition, users can only see posts, not post themselves into the group.
Other examples of leveraging Telegram as a data source include monitoring for:
Hate speech and death threats,
Hacking services for sale,
Exploit kits,
Data breaches,
Hate groups.
Using Telegram as an OSINT Source
As outlined above, are plenty of conversations of interest that happen through the Telegram app and its various groups. These groups can offer insight into criminal activity and better enable organizations to protect their assets and staff from emerging threats. For example, you might find information on a recent data breach through the app. Having this early knowledge of the breach is essential for mitigating costs.
However, as with any potential data source, it’s not a case of simply downloading the app. Efficiently scanning and monitoring the platform for potentially relevant or information of interest requires the right tools.
First, groups like Narcotic Express DE are closed groups, meaning locating and gaining access to them is a challenge in itself. Secondly, with features such as message self-destruct constant surveillance is necessary. These challenges mean time and resource need to be devoted to this specific channel, time and resource that might be better spent elsewhere.
Using an OSINT tool gives users the ability to access and utilize hard to reach data sources like Telegram. Data from Telegram is gathered by our data provider Webhose, who scrape the publicly available data from both open and harder to access closed groups continuously. Signal users can set up searches with Boolean logic, selecting Telegram as one of the data source options available.
12 of the Biggest Ransomware Attacks of 2020
Ransomware can cost an organization millions and often the victim has no alternative but to pay. In this article, we look at 12 of the biggest ransomware attacks that occurred in 2020.
Ransomware is a form of malware which is installed on a victims device or devices with the main objective of seizing and/or locking away sensitive data. As the name suggests in order for a victim to regain access to their data and systems they need to pay a ransom. More often than not, the two options a victim is presented with when they succumb to a ransomware attack is to either rebuild their systems from scratch and potentially have the attacker leak the data online - or pay up.
As such, it’s unsurprising that, in our increasingly digital age with more and more data on the cloud, that the number of attacks and the success of ransomware attacks is on the rise. Approximately 58% of ransomware victims paid in 2020, compared to 39% in 2017.
Ransoms for these kinds of attacks range from a few hundred dollars to thousands or even millions of dollars payable in cryptocurrency such as Bitcoin. In return for the payout, the attackers will release a decryption key allowing the organization to return to business. Certain industries, such as government organizations and hospitals are more susceptible to ransomware attacks due to the nature of the work that they do often being time-sensitive. For example, a ransomware attack crippled a hospital in Germany, leading directly to one patient’s death.
There are numerous strategies that ransomware attackers employ to gain access to a victims database. One of the most common though is through social engineering tactics, such as phishing emails. Cybercriminals can make these emails look exactly like trustworthy emails from official sources, tricking victims into downloading compromised software onto their device.
Because of the nature of social engineering tactics, and the evolving cyber threat landscape no organization can ever be fully secure from malware threats. Below we outline 12 of the biggest ransomware attacks that occurred in 2020.
12 Ransomware Attacks that Happened in 2020
1. ISS World
Estimated cost: $74 million
In February of 2020 ISS world, a Denmark based company went down due to a ransomware attack. Thousands of employees were left without access to their systems and emails. This cost them an estimated $74 million which includes regaining control of the affected IT systems and re-launching critical business systems.
2. Cognizant
Estimated cost: $50 million
A ransomware attack on the organization Cognizant in April of 2020 is said to have cost the company over $50 million, potentially as much as $70 million, including legal and consultation costs and data recovery costs, along with the financial loss reflected in their second-quarter earning in 2020.
3. Sopra Steria
Estimated cost: $50 million
The company Sopra Steria revealed that they were hit by hackers using a new version of the Ryuk ransomware in October.
They estimate that the fallout, including dealing with the various systems that went out of action, is likely to have a gross negative impact on operating margin of between €40 million and €50 million.
4. Redcar and Cleveland Council
Estimated cost: $14 million
Redcar and Cleveland Council in the UK suffered an attack on their systems in February of 2020 costing the council an estimated $14 million. The ransomware attack is said to have disrupted the company’s network, tablets, computers, and mobile devices for 3 full weeks. The council announced that in March, that it could take months for a full recovery and estimated the overall costs to be between $14 - $21 million.
5. Software AG
Estimated cost: $20 million
Software AG is the second-largest software vendor in Germany. They were reportedly hit with the Clop ransomware in an attack in October of 2020. The company disclosed that the ransomware attack disrupted a part of its internal network but didn’t affect customer services. The cybercriminal group responsible demanded a $23 million ransom.
7. Travelex
Estimated cost: $2.3 million
It was reported that Travelex the money exchange firm was hit with a file-encrypting malware attack which shut down its internal networks, website and apps for several weeks. Reportedly Travelex paid a ransom of $2.3 million in BTC to the dark actors to regain access to their data and restore services.
8. University of California San Francisco (UCSF)
Estimated cost: $1.14 million
UCSF was targeted by a malware attack which encrypted servers used by the school of medicine impacting students in June of 2020. The ransomware was prevented from travelling to the core UCSF network and causing more damage. The authorities negotiated with the cybercriminals and UCSF ended up paying approximately $1.14 million in ransom of the $3 million demanded.
9. Shirbit Insurance
Estimated cost: $1million
After a cyberattack on the Israeli Insurance provider Shirbit in December of 2020 the attackers demanded roughly $1 million in Bitcoin. In order to pressure the company into paying they demanded immediate payment or an increase in the ransom cost, doubling after 24 hours. Additionally, to show they weren’t empty threats they dumped the first 300 records online, again threatening to dump additional records every 24 hours until they received payment.
10. Communications and Power industries
Estimated cost: $500,000
California-based Communications & Power Industries (CPI) makes components for military devices and equipment, like radar, missile seekers and electronic warfare technology. The company counts the U.S. Department of Defense and its advanced research unit DARPA as customers. Reportedly, CPI paid $500,000 to obtain the decryption key to unlock their servers and return services.
11. Grubman Shire Meiselas & Sacks
Estimated cost: $365,000
Grubman Shire Meiselas & Sacks is a law firm that specializes in law for those in the media and entertainment industry. Their clients consist of a range of A-list celebrities and, with such high profile individuals on the line, the stakes for them were extremely high. They were targeted and files encrypted by REvil ransomware. The firm agreed to pay an estimated $365,000, however, the attackers started demanding more afterwards and the company has since kept quiet on what it has or is willing to pay.
12. Tillamook County
Estimated cost: $300,000
Tillamook county in the US was attacked by cyber attackers in January. The attack interrupted their email network, phone systems and website. After exhausting alternative options, they estimated the costs to restore service would cost well over $1 million and take several years and opted instead to pay the $300,000 ransom.
Keeping your data and organization secure
Never click on suspicious links or any links attached in unsolicited emails.
Back up systems and data continuously. Create a separate data-backup in an external hard drive that is not connected to your computer, so that you don’t have to pay the ransom if a ransomware attack happens.
Never disclose personal information over the phone or over email.
Educate employees of cybersecurity best practices and social engineering tactics that may be used against them.
Limit employee access to sensitive data to reduce attack surfaces.
OSINT Tools and Mitigating Costly Ransomware Attacks
Early warning of data beaches through OSINT tools can help you predict and prevent cyber attacks as well as enable organizations to take mitigating actions faster. While open-source intelligence tools can’t prevent ransomware, they can help organizations reduce the risks and potential damages.
OSINT tools can be used by organizations to monitor their supply chains, allowing them to learn of potential disruptions in real-time and enabling them to implement contingency plans fast.
Additionally, organizations can use tools like Signal to monitor for ransomware and malware currently being used. This can help security teams determine emerging threats being used against other organizations in their industry to better inform ongoing cybersecurity best practices.
Ultimately, by using OSINT to monitor darknet forums and market places security professionals are able to learn about the newest strategies being employed, the most recent weaknesses being exploited, and the most current software being utilized. Armed with this knowledge they are much more able to develop effective countermeasures as well as actively prevent ransomware infection.
5 Ways AI is Subtly Shaping the World as we Know it
AI is shaping our world in numerous ways from targeted ads to rapidly advancing facial recognition applications and even AI-generated malware.
Artificial Intelligence (AI) describes technologies that can make informed, non-random decisions algorithmically. It has many current and potential applications, it is the current pinnacle of humanities ceaseless drive towards greater and greater efficiency. In particular regard to OSINT though, it enables humans to collect, analyze and interpret huge sets of data, data sets so large that it would be entirely unfathomable to even approach them without machine assistance.
Everyone knows AI is shaping their world in one way or another. But often the changes are subtle, gradual and go unnoticed. Very few of us know what actually goes on behind the steel doors of the big tech companies like Alphabet, Facebook, and Apple. And yet we interact with their AI systems on a daily basis and those systems have huge power over our lives. In this article, we take a look at some of the key ways AI is being used today and how it will become increasingly important as our technologies improve.
5 Ways AI is Shaping the World
1. Improving and optimising business processes
The very first robots in the workplace were all about automating simple manual tasks. This is the age of factories and production lines. Today though, it’s not manual tasks that robots are taking over. Instead, software-based robots are taking on repetitive tasks carried out on computers.
Initially, this was limited to automating simple repetitive tasks, such as “send follow up email 2 if no response after 3 days”. This has already reduced admin tasks and improved business operational efficiencies immeasurably. The next step though is the use of AI technologies to further alleviate some of the more labour intensive ‘intelligent’ tasks such as data gathering, aggregating and analysis, leaving people to spend more time on complex, strategic, creative and interpersonal tasks.
2. More personalization will take place in real-time
Big tech companies are already using data to personalization services. Google Discover, for example, is a feed based on a complex algorithm which reads your online history and tailors the news feed to your particular interests. Other big tech examples are Spotify and Netflix which use AI to suggest relevant media based on your historical behaviour.
This technology is constantly being evolved and is probably one of the most noticeable in our day to day lives. The end goal is a system which can almost perfectly predict your desires and needs, an outcome none of us are likely to protest against. On the other side of the same coin though is the use of that very same data to target individuals with hyper-relevant ads. This practice can often seem intrusive and is one of the driving forces behind the adoption of VPN’s.
3. AI in the creative space
Some things are still, even in 2020, better handled by humans. That being said AI technologies are now beginning to encroach on the creative spaces. Scorsese's, The Irishman, is one example of this, where Robert De Niro was de-aged on-screen using AI technology.
There are additional uses though, for example, AI is being used to edit video clips for the purposes of spreading misinformation, and often these edits are incredibly hard to spot. This has led to a new sector of cybersecurity which requires AI technology to spot AI-generated or edited video and audio files.
4. Increasing AI in Cybersecurity
Even as data grows and is used to progress the development of AI this simultaneously opens up new avenues for exploits by threat actors. For example, AI can be used to create and automate targeted ‘intelligent’ phishing campaigns. AI-supported cyberattacks though have the potential to go much further. As such, increasingly advanced AI is needed to combat the evolving cyber threat landscape.
Related: How Machine Learning is Changing Modern Security Intelligence
5. AI learning to perfectly emulate humans
Anyone that keeps their eye on the work that Google is doing will know about their 2019 update, BERT. A natural language processing (NLP) framework which is designed to better understand context and intertextual reference so that they can correctly identify both the searcher's intent as well as the intent behind any content created.
One of the key challenges that faces AI right now is idiomatic or referential speech; language that has more depth of meaning, for example, determining the importance of the concept of a mother, or understanding a phrase like “six feet under”. Our current research and development project at Signal is one example of the practical applications of overcoming this challenge. It involves using machine learning to enable our software to understand the intent behind text, even when ‘hidden’ behind challenging language like idioms, to more accurately identify threats.
As these natural language processes advance, so too will conversational AI bots, to the point where, because of the range and complexities of their answers, you would be forgiven for mistaking them as human.
The Future of AI and what that means for OSINT
Artificial Intelligence, machine learning, and automation have already revolutionized intelligence gathering. With OSINT tools like Signal security teams and intelligence agents can effectively and efficiently monitor the open, deep, and dark web, setting up customized alerts based on searches that leverage boolean logic. Machine learning takes this intelligence to the next level. It allows for vast amounts of data to be collected, aggregated, and for all the irrelevant hits to be essentially culled, supplying the security team at the end with actionable, relevant intelligence.
Humans play an essential role in this new intelligence lifecycle. In defining the search terms to match security strategies, analysing the end date the system feeds back, reassessing the searches based on the new evidential data and implementing appropriate responses. This is a key role that will no doubt evolve as the technology becomes more accurate, reducing inefficiencies in process.
How Machine Learning is Changing Modern Security Intelligence
Today, AI and machine learning enable both attackers and defenders to operate at new magnitudes of speed and scale. Security teams need to leverage the power of machine learning and automation if they want to stand a chance of mitigating threats.
A key challenge facing modern security teams is the explosion of new potential threats, both cyber and physical, and the speed with which new exploits are taken advantage of. Additionally, in our globalized world threats can evolve from innumerable sources and manifest as a diverse range of hazards.
Because of this, security teams need to efficiently utilize automation technology and machine learning to identify threats as or even before they emerge if they want to mitigate risks or prevent attacks.
Artificial Intelligence in the Cyber Security Arms Race
Today, AI and machine learning play active roles on both sides of the cybersecurity struggle, enabling both attackers and defenders to operate at new magnitudes of speed and scale.
When thinking about the role of machine learning for corporate security and determining the need, you first need to understand how it is already being used for adversarial applications. For example, machine learning algorithms are being used to implement massive spear-phishing campaigns. Attackers harvest data through hacks and open-source intelligence (OSINT) and then can deploy ‘intelligent’ social engineering strategies with relatively high success rate. Often this can be largely automated which ultimately allows previously unseen volumes of attack to be deployed with very little effort.
Another key example, a strategy that has been growing in popularity as the technology evolves, making it both more effective and harder to prevent, is Deepfake attacks. This uses AI to mimic voice and appearance in audio and video files. This is a relatively new branch of attack in the spread of disinformation and can be harnessed to devastating effect. For example, there are serious fears of the influence they may bring to significant future political events such as the 2020 US Presidential Election.
These are just two of the more obvious strategies currently being implemented in a widespread fashion by threat actors. AI supported cyberattacks though have the potential to go much further. IBM’s DeepLocker, for example, describes an entirely new class of malware in which AI models can be used to disguise malware, carrying it as a ‘payload’ to be launched when specific criteria are met - for example, facial recognition of its target.
Managing Data Volumes
One of the primary and critical uses of AI for security professionals is managing data volumes. In fact, in Capgemini’s 2019 cybersecurity report 61% of organizations acknowledged that they would not be able to identify critical threats without AI because of the quantities of data it is necessary to analyze.
“Machine learning can be used as a ‘first pass’, to bring the probable relevant posts up to the top and push the irrelevant ones to the bottom. The relevant posts for any organization are typically less than 0.1% of the total mass of incoming messages, so efficient culling is necessary for the timely retrieval of the relevant ones.” - Thomas Bevan, Head Data Scientist at Signal.
Without the assistance of advanced automation softwares and AI, it becomes impossible to make timely decisions - impossible to detect anomalous activity. The result of which is that those organizations who don’t employ AI and automation softwares for intelligence gathering often miss critical threats or only discover them when it’s too late.
Signal OSINT and Machine Learning
Signal OSINT platform uses machine learning and automation techniques to improve data collection and aggregation. The platform allows you to create targeted searches using Boolean logic, but it is our machine learning capabilities which allow us to go beyond Boolean keyword searches.
“By recognising patterns in speech and relations between commonly used words, one can find examples of relevant posts even without keywords. While phrases like ‘I’m gonna kill the boss’ can be picked up by keywords easily, keyword searches alone struggle with more idiomatic speech like, ‘I’m gonna put the boss six feet under’, and will incorrectly flag posts like ‘Check out the new glory kill animation on the final boss’. Machine learning, given the right training data, can be taught to handle these sorts of examples,” says Thomas Bevan.
Signal continuously scans the surface, deep, and dark web and has customizable SMS and Email alert capability so that security teams can get real-time alerts from a wide array of data sources such as Reddit, 4Chan, 8Kun etc. Additionally, Signal allows teams to monitor and gather data from dark web sources that they would otherwise be unable to access either for security reasons or because of captive portals.
Finally, the software allows users to analyze data across languages and translate posts for further human analysis. There are additional capabilities, such as our emotional analysis tool Spotlight, which can help indicate the threat level based on language indicators.
Complementing AI with Human Intelligence
In order to stay ahead of this rapidly evolving threat landscape, security professionals should be using a layered approach that pairs the strategic advantages of machine learning to parse through the vast quantities of new data with human intelligence to make up for current flaws in AI technology.
Machines have been at the forefront of security for decades now. Their role though is evolving as they get passed the heavy lifting, allowing analysts and security professionals to analyse hyper-relevant data efficiently.
Why organizations need threat intelligence tools as part of their security defences
Threat intelligence is an essential tool for any security team. It is the gathering of evidence-based knowledge to inform action-oriented preventative and reactionary responses to an ever-evolving cyber threat landscape.
What is Threat Intelligence?
Those very same technologies that have allowed globalization, which have brought us all closer together and enabled organizations and brands to achieve the current growth and success they enjoy today, have simultaneously brought with them increased risks. These risks come in the form of increased vulnerabilities and exploitable attack vectors for cyber attackers. Threat intelligence is all about gathering data and knowledge to combat and mitigate these threats.
Threat intelligence provides organizations with information and context required to effectively predict and even prevent cyberattacks. Additionally, it helps inform security teams of the best practice for both preventative measures and response measures to ensure if there is a cyberattack the resulting costs are minimal.
In short, threat intelligence is the gathering of evidence-based knowledge to inform action-oriented preventative and reactionary responses to an ever-evolving cyber threat landscape.
The Importance of Threat Intelligence
Threat actors are increasingly persistent, and their persistence pays off. Even the most dedicated professionals can’t help but struggle to keep abreast of every new cybersecurity development. New exploits are constantly being discovered or developed and strategies such as social engineering are increasing in complexity. Security teams need up to date data and intelligence on evolving threats if they are going to be able to develop effective responses.
Additionally, within the corporate world one of the key buzzwords of the last two decades has been “accessibility”. Accessibility to data means organizations have necessarily become reliant on digital processes and almost everything is stored on the cloud. Unfortunately, while accessibility is essential to developing efficient processes, and effectively using big data, it also increases the number of threat vectors that attackers can exploit. According to the IBM 2020 data breach report the longer a data breach goes undetected the more expensive it ends up being for the organization. Primarily then, threat intelligence gathered using tools like Signal OSINT can help organizations detect data breaches earlier, mitigating the eventual costs both reputational and monetary.
The final reason that threat intelligence plays such a pivotal role in today’s security is the distinct lack of skilled cybersecurity professionals. Threat intelligence is a time-consuming business that requires a skilled deft hand to manage. The best threat intelligence solutions use machine learning to automate data collection, then filter and structure data from disparate sources to present only hyper-relevant information to a skilled security team for final analysis. The security team can then use this data to create effective actionable plans based on evidential knowledge. This approach optimizes the performance of both the cybersecurity professional and the intelligence tools being used.
Threat intelligence is actionable — it’s timely, provides context, and is able to be understood by the people in charge of making decisions.
Use Case Examples for Threat Intelligence
Threat intelligence can be used in a diverse range of strategies which makes it an essential tool for security teams in any organization. It’s most immediate value is in helping prevent an attack by gathering intel on threats in real-time, however, it’s also useful for a broad scope of activities such as managing vulnerabilities, informing decision making, and responding to attacks as or after they happen.
Related: The Role of Threat Intelligence and Cybersecurity in Retail
Prevent an attack
From the time that a vulnerability is found to the time an exploit targeting that vulnerability is available for threat actors is shortening. Security professionals need to know about the vulnerability fast so that they can implement a patch and prevent it from being exploited.
Respond to a Data Breach
Data breaches are costly and often go unnoticed. With the right threat intelligence tools you can determine when a data breach happens fast and take suitable actions to mitigate the costs of any following repercussions.
Manage a Vulnerability
The approach of “patch everything, all the time” is impractical and will likely see organizations fall behind - leaving more serious vulnerabilities open for longer. Threat intelligence can help security teams effectively manage vulnerabilities by giving the salient data to allow them to prioritize patches based on actual risk.
Risk Analysis
This leads on nicely from the last point. Threat intelligence can help security teams determine the actual risks associated with potential vulnerabilities or attacks by providing additional contextual information. For example, threat intelligence can help security professionals answer the following questions:
Which threat actors are using this attack, and do they target our industry?
How often has this specific attack been observed recently by enterprises like ours?
Which vulnerabilities does this attack exploit, and are those vulnerabilities present in our enterprise?
What kind of damage, technical and financial, has this attack caused in enterprises like ours?
Fraud Prevention
Fraud can encompass anything from a fraudulent use of your brand, data, or even impersonation of your employees. For example, an individual might impersonate a doctor and sell fake versions of your prescription medication online.
Incident Response
Having the ability to gather and filter through threat intelligence from across the surface, deep, and dark web in real-time allows security teams to effectively and appropriately respond to incidents as they are happening.
How can Signal threat intelligence improve your organization’s security?
Signal allows our customers to analyze emerging global trends, detect threats in real-time, and then form appropriate security strategies to counter these potential threats as or even before they fully reveal themselves.
One of the key issues that security teams and analysts face is the sheer amount of noise that might surround their brand. Invariably much of this noise is irrelevant to their purposes, however, some of it will be bad. This is why Signal assists with advanced filters with boolean logic as well as features such as our emotional analysis tool.